Mukri Chavande
About
-
Posted Answers
Answer
The Tri-Oval Oxidation Ditch System provides superior wastewater treatment process control and design" · Uploaded by Aeration Industries
Answer is posted for the following question.
Answer
New to the cloud? Azure fundamentals is a six-part series that teaches you basic cloud concepts, provides a streamlined overview of many Azure services, and
Answer is posted for the following question.
What is microsoft azure fundamentals certification?
Answer
The technique requires attackers to have physical access to computers and also assumes the target has not configured their system to protect the Intel Management Engine BIOS Extension (MEBx) account on PCs that support Intel’s Active Management Technology (AMT).
AMT is Intel’s remote maintenance feature used on Intel vPro-enabled and Xeon processors. MEBx is a BIOS extension used to manually configuring the AMT service. When configured properly, MEBx is password protected.
Researchers at F-Secure, who outlined their research in blog post Friday, said typically users don’t change the MEBx password from the default password “admin”.
“The issue allows a local intruder to backdoor almost any corporate laptop in a matter of seconds, even if the BIOS password, TPM Pin, Bitlocker and login credentials are in place,” F-Secure wrote.
The attack starts with a reboot the target’s laptop into the PC’s boot menu. Typically, an adversary would not be able to bypass a BIOS password, stopping the attack in its tracks, said researchers.
“In this case, however, the attacker has a workaround: AMT. By selecting Intel’s Management Engine BIOS Extension (MEBx), they can log in using the default password ‘admin,’ as this hasn’t most likely been changed by the user. By changing the default password, enabling remote access and setting AMT’s user opt-in to ‘None’, a quick-fingered cyber criminal has effectively compromised the machine,” F-Secure wrote.
This allows the attacker to configure the targeted laptop for remote access later. The one caveat, in order for the attacker to access the laptop remotely it must be able to “insert themselves onto the same network segment with the victim,” according to the research. “Enabling wireless access requires a few extra steps,” they said.
Researchers acknowledge the physical proximity required in the attack limits its potential threat. However, F-Secure researcher Harry Sintonen said there are scenarios where a mix of social engineering combined with the short time needed to conduct the hack can leave some vulnerable.
“Essentially, one attacker distracts the mark, while the other briefly gains access to his or her laptop. The attack doesn’t require a lot of time – the whole operation can take well under a minute to complete,” Sintonen said.
Intel has responded to F-Secure’s research stating publicly it can’t help it if “some system manufacturers have not configured their systems to protect Intel Management Engine BIOS Extension (MEBx).”
Justin Jett, director of audit and compliance for Plixer, a network traffic analytics firm, said attacks utilizing this method could be effective.
“The Intel AMT security issue is very feasible. Rogue employees who have access to many computers in a corporation and who share the same network space as their colleagues, could take advantage of this vulnerability,” Jett said.
He said the loophole could be closed with a BIOS firmware update to prevent circumventing normal BIOS protocols. “The main objective of organizations in the meantime should be to update systems so they are not using the default password, and to review network traffic analytics data for connections over the Intel AMT ports.”
F-Secure recommends following Intel’s best practices for the AMT feature (PDF) or disabling it completely.
Concerns over the Intel Management Engine have been ongoing for years. In May, Intel patched a critical vulnerability that dated back nine years in the company’s Active Management Technology, which is based on Intel ME. That vulnerability could allow an attacker to gain remote access to AMT services such as the keyboard, video and mouse (KVM), IDE Redirection, Serial over LAN, and BIOS setup and editing.
In November, Intel released patches to protect millions of PCs and servers from vulnerabilities found in its Management Engine that could allow local attackers elevate privileges, run arbitrary code, crash systems and eavesdrop on communications. In August, Positive Technologies published a report on how the US government can disable ME and the public can’t.
Suspicions date back to 2012 over Intel’s implementation of AMT with some labeling it a “backdoor enabled by default.” A reported flaw identified in June 2016 by researcher Damien Zammit claimed that there was a remotely exploitable security hole in the Intel Management Engine that created a secret backdoor allowing a third party to use undetectable rootkits against Intel PCs. Intel denied such claims.
Answer is posted for the following question.
what is mebx hotkey?
Answer
YTONG is the world's largest manufacturer of aerated concrete blocks and the only Those who build using YTONG aerated concrete rely on a great deal of
Answer is posted for the following question.
How to make ytong block?
Answer
Benefits: Warrior II strengthens the legs, opens the hips and chest . Warrior II develops concentration, balance and groundedness. This pose improves
Answer is posted for the following question.
What is warrior 2 pose in yoga?
Answer
Unearth the vibrancy of Whyalla at local events, markets, visiting shows and . Whyalla's most unique event occurs May - August every year with the arrival of the .
Answer is posted for the following question.
What's happening in whyalla?
Answer
Alcohol and Drug Addictions: Psychology - ACCREDITED CERT,Udemy.
4 ☆ / 5
To download tutorial or watch: Alcohol and Drug Addictions: Psychology - ACCREDITED CERT
Why this tutorial?
Udemy Alcohol and Drug Addictions: Psychology - ACCREDITED CERT
Note: Learn psychology of human behaviour related to addictions, alcohol- and drug treatments, diagnose & symptoms, overdose. Elmira Strange, MPhil, Dip is the instructor of this tutorials.
To download tutorial or watch: Alcohol and Drug Addictions: Psychology - ACCREDITED CERT
Benefits from this tutorials
- Have an ability to explain human behaviour related to 'addictions'
- Understand what 'drug' and 'alcohol' symptomatology and treatments are
- Use the knowledge from the course in your current work, study, career
- Add the course accomplishment to your CV / Resume!
To download tutorial or watch: Alcohol and Drug Addictions: Psychology - ACCREDITED CERT
Video Tutorial Details
Are you interested in learning about psychology of addictive behaviour? Would you like to help others through your work?
In this course you will take 26 informative lectures where you will learn:
What the signs and symptoms of addiction are
How 'addictions' get diagnosed
What kind of drugs people take (that makes them 'addicted')
What psychological and medical treatments available to people diagnosed with addiction are
The steps to full recovery from addictions
You will also understand:
What 'detoxification treatment' is
Withdrawal from the substance and how it is experienced
What 'overdose' by drugs is and how often it happens
and so much more!
Are you ready to start your learning?
Then I’ll see you in my class!
P.S. This course is now fully accredited by the IAOTH - International Association of Therapists!
P.P.S. At the end of the course you will see the instructions on how to obtain your certificate of completion
Who this course is for:
- Anyone who wants to learn more about 'addictions'
- Anyone who is interested in human mind and behaviour
- Anyone who wants to understand psychology of 'addictions'
- Students of psychology, counselling, psychotherapy
- Professionals working in caring or mental health settings
To download tutorial or watch: Alcohol and Drug Addictions: Psychology - ACCREDITED CERT
Answer is posted for the following question.
How Can We download or watch Udemy Alcohol and Drug Addictions: Psychology - ACCREDITED CERT video tutorials for free?
Answer
Feldman added that Shaq is close to making the investment , saying that it is now a matter of "dotting the i's and crossing t's'' BKFC was only
Answer is posted for the following question.
How to invest in bkfc?
Answer
Yadav Kirana Shop Roy chicken fried steak
Raipur, Chhattisgarh
Answer is posted for the following question.
Where was the best Chicken Fried Steak in Raipur, Chhattisgarh?
Answer
Phonetic: Test your pronunciation on words that have sound similarities with 'ceja': sayed · celia · satya · sawa
Answer is posted for the following question.
How to pronounce ceja?
Answer
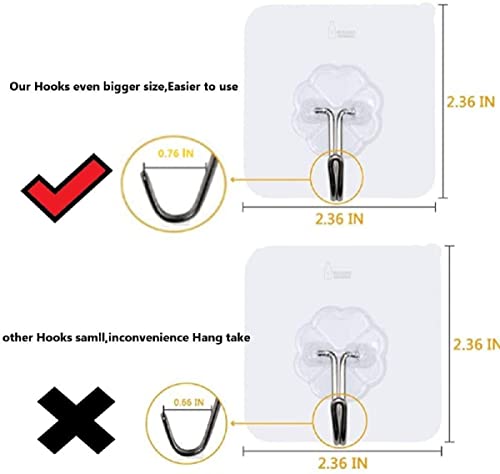
Purchased Price: Rs 179 INR from Amazon India
REVIEW
The product works well.It's a must buy, at this price.Thanks for providing a quality product.
Answer is posted for the following question.
Review this Jialto Adhesive Hooks Kitchen Wall Hooks-Heavy Duty 13.2lb(Max) Nail Free Sticky Hangers with Stainless Hooks Reusable Utility Towel Bath Ceiling Hooks-10 pcs [Review]?
Answer
To become a Group-A officer in CBI, you have to become an IPS officer by passing the Civil Services Examination conducted by UPSC . To become a sub-inspector in CBI, you have to take SSC CGL exam. In CBI Sub Inspector Test (SSC CGL), Tier 1 and Tier 2 examinations are of objective type.
Answer is posted for the following question.
How to be cbi officer in india?
Answer
Purchased Price: Rs 803 INR from Amazon India
REVIEW
It was deep from the back sides.The straps of porn will come out.The blouse is loose and the sleeves are tight.The stitch was improper with the measurements.The other blouse I bought was very nice.
Answer is posted for the following question.
This festival should I purchase STUDIO Shringaar Women's Brocade Elbow Length Sleeves Saree Blouse [Review]?
Answer
Check Following Video
Answer is posted for the following question.
How to mtb jump?
Answer
- Step 1: Acquire Digital Signature Certificate (DSC)
- Step 2: Acquire Director Identification Number (DIN)
- Step 3: Create an account on MCA portal- New user registration @ mca.gov.in.
- Step 4: Incorporate or Apply for the company to be registered.
Answer is posted for the following question.
How to register name of business?